Mystery Check

How easy is it for an attacker to really get into your company – without being detected?
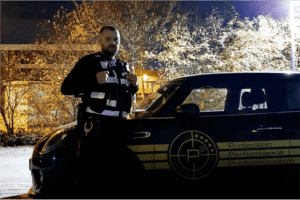
Red Teaming – Real attack simulation – Detection critical vulnerabilities
Most security concepts work on paper.
The decisive factor is whether your measures actually hold up in everyday life.
As part of a mystery check, your company is specifically tested under real conditions – covertly, in a structured manner and from the perspective of a potential attacker.
How to recognize,
- how far an attacker would actually get
- which safety measures are effective
- and where specific weaknesses exist
The focus is on a realistic review of existing safety measures under actual operating conditions.
The behavior of potential attackers is simulated in order to make real risks visible. This includes in particular
- Unauthorized entry into buildings
- Bypassing access controls
- Exploiting organizational weaknesses
- Social engineering towards employees
- Movement within the object up to sensitive areas
This gives you a clear and reliable assessment of your actual security situation.
Identification of realistic attack scenarios
Concealed implementation under real conditions
Checking the effectiveness of your current measures
Detection of critical vulnerabilities
Documentation of real attacks
Concrete recommendations for action
Scope of services
The following services form the framework of the covert security check.
The aim is to test all relevant and realistic attack scenarios under real conditions – not in theory, but in practice.
The implementation is deliberately flexible and iterative to enable a complete assessment of your security measures. measures.
This gives you a realistic and reliable assessment of your actual security situation
Project approach and milestones
The project is structured and implemented along defined milestones.
The procedure is designed to check and systematically evaluate your safety measures under realistic conditions.
Processing is based on relevant attack scenarios so that vulnerabilities can be specifically identified and converted into reliable findings.
What you get in the Mystery Check
The mystery check is made up of clearly defined service modules – from the development of realistic attack scenarios to the concrete derivation of measures. On request, P3 can also take over the further implementation for you.
Development of realistic
attack scenarios
Implementation covert
security checks
documentation and analysis
of real weak points
Derivation of concrete
optimization measures

THIS IS HOW THE MYSTERY CHECK ACTUALLY WORKS
The mystery check follows a clearly structured procedure that takes into account all security-relevant areas of your company.
The focus is on practical testing of the interaction between people, technology and organization under real conditions.
The process is divided into the following phases:
- Kick-off & target definition
- Scenario development & attack conception
- Concealed implementation (red teaming)
- Analysis, measures & handover
WHY NOW?
The biggest security gap is the one you don’t know about.
Many security incidents are not caused by a lack of technology, but by undetected weaknesses in the interaction between people and the organization. In everyday life, security measures are frequently circumvented – often unnoticed. It is precisely these gaps that are exploited by attackers.
Without a realistic review, it remains unclear how effective your existing measures actually are.
The crucial question is not whether these vulnerabilities exist – but whether you recognize and close them in time.
YOUR GLOBAL PARTNER IN PREMIUM SECURITY SOLUTIONS.